The High Performance Story: How MAYASEVEN Delivers Elite Cybersecurity
In today’s threat landscape, businesses need a cybersecurity partner they can trust to protect their most critical assets. MAYASEVEN has emerged as an industry leader by consistently delivering high performance penetration testing, red teaming, and cybersecurity services to help clients safeguard their systems and data.
Proven Track Record of Excellence
MAYASEVEN has an impressive track record of successfully identifying and mitigating vulnerabilities for clients across industries. Our team of highly skilled ethical hackers and security professionals leverage cutting-edge tools and techniques to provide comprehensive security assessments. With hundreds of penetration tests and red team engagements completed, we have helped companies of all sizes enhance their security posture and defend against even the most sophisticated cyber threats.
Our focus on technical excellence, attention to detail, and commitment to exceeding client expectations set us apart. MAYASEVEN’s rigorous methodology ensures thoroughness and quality in every assessment we perform. Clients consistently praise the depth and actionable insights provided in our reports and deliverables.
Dedicated to Quality and Security
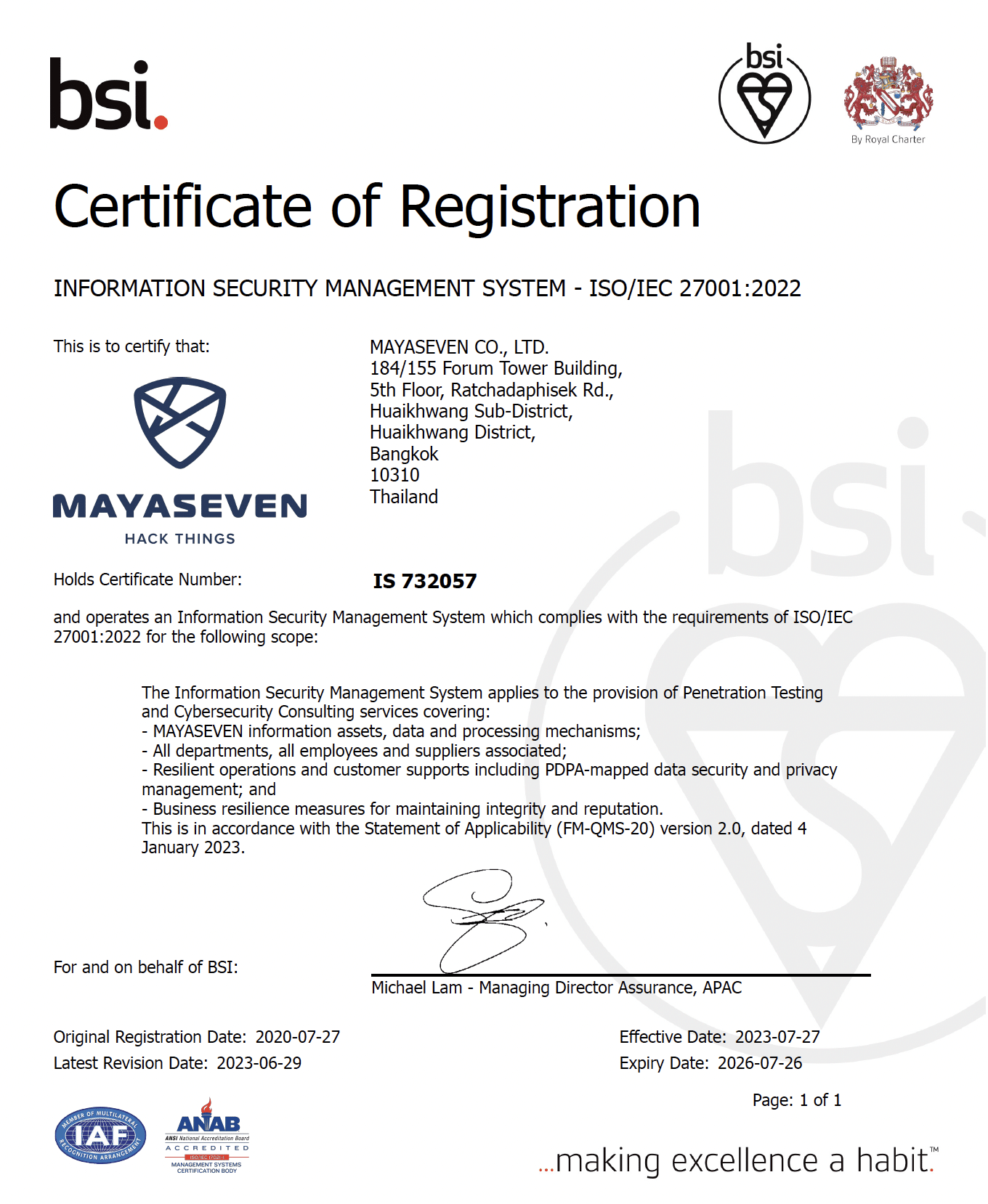
At MAYASEVEN, we understand the importance of maintaining the highest standards of quality and security in our services. We are proud to announce that we have achieved certifications for ISO 9001:2015 and ISO/IEC 27001:2022. These internationally recognized certifications demonstrate our commitment to delivering top-tier services while safeguarding the confidentiality, integrity, and availability of our clients’ information.
The ISO 9001:2015 certification validates our adherence to a robust quality management system, ensuring that we consistently meet client requirements and continuously improve our processes. The ISO/IEC 27001:2022 certification affirms our implementation of a comprehensive information security management system, showcasing our dedication to protecting sensitive data and maintaining the highest level of information security.
These certifications not only provide assurance to our clients but also reflect our unwavering commitment to excellence and security in everything we do.
Unmatched Expertise
MAYASEVEN’s team is our greatest asset. We’ve assembled an elite group of certified security professionals with deep expertise across offensive security disciplines. Our consultants hold top industry certifications including OSCP, OSCE, and GXPN, and have backgrounds ranging from former military cyber operators to seasoned penetration testers.
Continuous learning is ingrained in our culture. We invest heavily in training, research, and development to stay on the cutting edge of attacker tradecraft. Our clients benefit from our team’s collective knowledge and insights gleaned from conducting hundreds of assessments across industries.
Whether it’s a targeted penetration test, purple team exercise, or multi-month red team operation, MAYASEVEN has the expertise to simulate real-world attacks and help harden defenses against them. There is no security challenge our team isn’t equipped to tackle.
Advancing the Industry
MAYASEVEN is committed to advancing the state of the cybersecurity industry. We actively contribute to the security community through research, open-source tools, and thought leadership.
Our consultants are frequent speakers at top security conferences where we share our latest techniques and ideas. We’ve released numerous open-source tools downloaded by thousands of practitioners worldwide. And our blog and whitepapers offer expert analysis on the latest threats and defensive strategies.
By openly sharing knowledge, we aim to raise the bar for the entire industry. Our leadership has established MAYASEVEN as a trusted voice on the frontlines of cybersecurity innovation and tradecraft.
Experience the MAYASEVEN Difference
Comprehensive penetration testing and cybersecurity services require a provider that combines elite talent, time-tested methodologies, and dedication to client success. MAYASEVEN has mastered this rare combination.
Our track record of results for the world’s leading organizations, coupled with our ISO 9001:2015 and ISO/IEC 27001:2022 certifications, sets us apart as a trusted and reliable cybersecurity partner.
If you’re looking for a high-performance security provider that will relentlessly protect your business, contact MAYASEVEN today. Experience the difference of a true industry leader.
Reference: