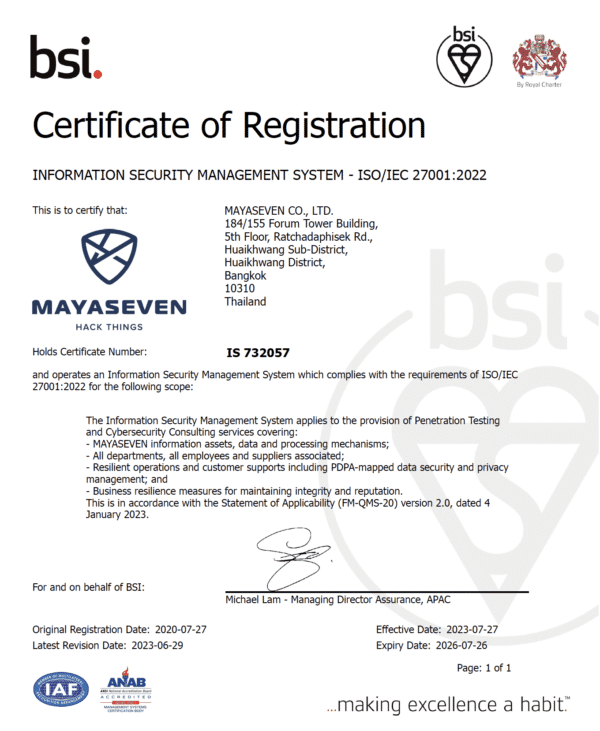
MAYASEVEN is ISO/IEC 27001:2022 Certified
MAYASEVEN has accomplished ISO/IEC 27001:2022, the international standard for information security management system. We commit to follow the highest standard in quality of services and data security throughout the organization. Therefore, our ISMS has designed to prioritize our clients’ data confidentiality at the highest level.
MAYASEVEN ISMS Program
The main principles of MAYASEVEN’s ISMS program is to ensure the confidentiality, integrity and availability of any type of information that we process, store and communicate. This following table summarizes the ISMS policies and how we implement them to achieve the goals of the program.
ISMS Policies
• Integrated management system (IMS) to streamline and simplify the application of ISO 9001:2015 and ISO/IEC 27001:2022 resulting in robustness implementation
• Sophisticated PDCA application with international framework mapping
• Client-centric solution from internal and external contexts
• Fulfill the needs of and contractual obligations to clients and interested parties
• Employee competence, enthusiast, and awareness strengthening to maximize quality of service
• Consolidate national and international standard, procedure
• Internal and external audits to ensure integrity, reliability, and reputation
• Continual improvement by maturity model according to consolidation of international standard, procedure, research, and framework
• Social responsibility with our heart of contribution beyond society
ISMS Implementation
• Structured organization of information security
• Risk management: fully integration with asset and in-depth process analysis
• Human resource security
• Asset management
• Access control
• Physical and environmental security
• Operations security
• Communications security
• System acquisition, development and maintenance
• Supplier management
• Incident response plan
• Business continuity
• Compliance: PDPA, local, and international regulation
We Ensure Secure Environment of Your Data
Conduct Regular Penetration Testing
We conduct regular penetration testing on our internal infrastructure and software. This is part of our security management and maintenance standard to protect our client’s data secure environment from external threats internal threats by simulating the attack on every possible attack surfaces to identify the vulnerabilities on our system and strengthen them promptly. We also have a screening process before we adopt any software to our system to mitigate the risks from using the software to maintain the security of the environment to the highest level.
Data in Transit Encryption
For each of our employees has mail certification from a trusted certification authority (CA); the communication from us is always signed by the sender to guarantee the sender’s identity digitally. All sensitive and confidential information only are transferred on a secure channel with the mail encryption algorithm, S/MIME, or secure file encryption algorithm.
Deletion Policy
We delete all data related to client projects as soon as possible, up to one year, or as per the client’s request, to prevent data breach incidents.
Data retention
We only keep all data related to client project for only one year. After that, we will dispose of that data. With this, we can reduce the risk of sensitive data loss.
Secure Storage Media
All clients’ data are only processed and stored on a controlled secured media that have security mechanisms and encryption on the hardware level to protect the data from being unauthorizedly accessed and being compromised by external threats.
Security Measures
Operation Security
Endpoint Detection and Response
Every device that processes or stores sensitive information has an Endpoint Detection and Response (EDR) system integrated on them. The EDR can prevent threats and maintain security within the organization.
A clean environment for processing
We have a high standard secure device to process the data, and also process them in the virtual environments, which isolate the processed data from the host device. The virtual environment is cleaned to its original state every time after the data is processed to reduce the old data leaking to another client’s data processing.
Software whitelisting
Our data processing devices have restricted rules for software installation to minimize the threat surface on every possible point. Our software selection has many criteria that cover every perspective for our clients to ensure their data is safe.
Certified identity
When we send an email to clients, we have digital signature to ensure our integrity and non-repudiation.
Physical Security
Building access
Our building has access control who is entered and when the person is entered.
Workplace security
Our workplace has access control (such as fingerprint scan) that our employees can enter only and also have security cameras that keep the record as ISO standard.
Data and document disposal
We have access control to our client’s reports. Only the person who is responsible for the project can access the report. Also, we use document disposal methods that secure our client information.
Secure asset management
We have asset management to identify the risks of our systems, including our client data.
HR Security
Background check
Our employees must pass the background checking process with zero criminal records with every position they applied. Also, our employees must have their credit score checked by National Credit Bureau (NCB) as well.
Explicit contract
Our employees have to sign non-disclosure agreements (NDA) that state information security, confidentiality, and policies.
Internal communications
Every internal communication via email is encrypted. Furthermore, we have a tracking system about the information sent between employees.
Access on a need to know basis
Our employees have a restricted access to the client’s data associated with the project. The employees who are not involve in the project will not be able to access that client’s information.

